Azure Bicep
Azure Bicep
Share Bicep modules with private registry
A common problem for many organizations is to share and consume infrastructure templates. Many ended up with a storage account in Azure, but that had some limitations around versioning and sharing of secrets. Directly consuming templates from a Git repository is another option. However, that’s not exactly problem-free either. For example, what happens if a colleague makes changes, and you reference the template without knowing what has changed. In the best case, a missing parameter will fail your pipeline. In the worst case, you have downtime.
The key concept of having Bicep modules in a common store is for everyone inside your organisation to use these modules when they’re provisioning infrastructure. Picture this scenario. Multiple development team is often using the same type of resource, like Azure SQL, Azure Functions, storage accounts, etc. Your organization likely have a few governance rules applied. Like tagging strategy, allowed SKU, different configuration for test and production and so on. Pre-created and easially consumable modules taking care of this is what you need. Azure Container Registry for Bicep files is now available.
Azure Bicep private registry
With Azure bicep version 0.4.1008 you have a built-in option to publish your Bicep modules to a private registry. The private registry is not a new resource type, in fact, you are uploading your Bicep files to Azure Container Registry which allows you to leverage versioning which will make sure you do not break templates for everyone each time people make changes. Once your Bicep module is uploaded to ACR everyone with permission to pull images can use your modules.

Upload Bicep modules to ACR
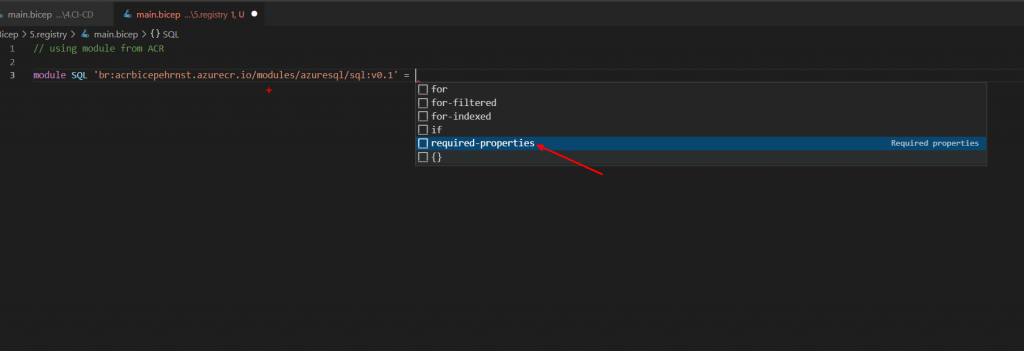
A shared bicep module is used in the same way as a local module, but instead of the local path, you specify the URL and version of the file within the registry. More on that later.
Assuming you already have one Bicep module or a set of them, you only need to provision a container registry. To push the “image” you need acrPush permissions and to consume you need acrPull. Below is the syntax used for uploading a bicep file to ACR.
az bicep publish storage.bicep --target br:exampleregistry.azurecr.io/bicep/modules/storage:v1I am using this code base against my existing registry, so my command to upload is as follows;
bicep publish .\Bicep\3.modules\sql.bicep --target "br:acrbicepehrnst.azurecr.io/modules/azuresql/sql:v0.1"No response is given on successful upload, but to make sure everything is alright we can confirm with this PowerShell command, which will list all repositories in your registry.

Get-AzContainerRegistryRepository -RegistryName acrbicepehrnstUsing modules from the registry
Including modules from a private registry is as easy as using local modules. With Bicep extension enabled in VSCode, you also get validation of the remote modules.
pssst… if you by any change use EMACS you can have the same through LSP and Bicep Lang server
var tags = {
'owner': 'Martin Ehrnst'
'purpose': 'Bicep demo'
}
module SQL 'br:acrbicepehrnst.azurecr.io/modules/azuresql/sql:v0.1' = {
name: 'sqlDeploy'
params: {
databaseName: 'moduletest'
dbAdId: '8776fb6e-5de0-408c-be03-c17a67b079d0'
dbAdLoginName: 'name@company.com'
env: 'prod'
tags: tags
}
}Summary
In this post I have showed you the core concept, how you upload and how you consume the modules. To me this is only half the story. In my next post I will go through how we can put everything inside a pipeline and add a better versioning to the modules.
Azure Bicep private registry is probably here to stay. Upuntil now it is the best solution to share infrastructure templates within an organization.